The Problem
AI adoption in the enterprise is accelerating — but security and compliance teams are hitting the brakes. And for good reason. Most AI tools are built for speed-to-market, not for the rigorous data governance requirements that enterprises operate under. The result is a growing tension between business units eager to unlock AI productivity and IT and security leaders responsible for protecting sensitive data, maintaining regulatory compliance, and preserving customer trust.
The core fear isn't unfounded. Many AI platforms process and store data on shared infrastructure, use customer conversations to improve their models, and require broad permissions that exceed what users actually need. For organizations operating in regulated industries — finance, healthcare, government, legal — this isn't just a policy concern. It's a disqualifying risk.
What makes this particularly frustrating is that the business value of enterprise AI is real and measurable. The problem isn't the technology itself. It's the architecture. Organizations shouldn't have to choose between AI capability and security posture — but without a deliberate governance framework, that's exactly the tradeoff being forced on them.
The Solution
The answer lies in a security-first AI architecture that treats data sovereignty, identity, and access control as foundational — not afterthoughts bolted on post-deployment.
Data Residency by Design Rather than sending data to external servers or shared cloud infrastructure, a governed AI deployment runs entirely within the customer's own environment. Conversations, documents, and model outputs stay inside the organization's cloud account — never leaving the perimeter. This isn't a configuration option; it's the default architecture.
Identity Provider Integration Governed AI connects to your existing identity infrastructure — SSO, SAML, OIDC — so user provisioning and deprovisioning happens automatically through the same workflows already managing access across the enterprise. There are no separate user directories to maintain, no orphaned accounts to audit. When an employee offboards, their AI access revokes in lockstep with everything else.
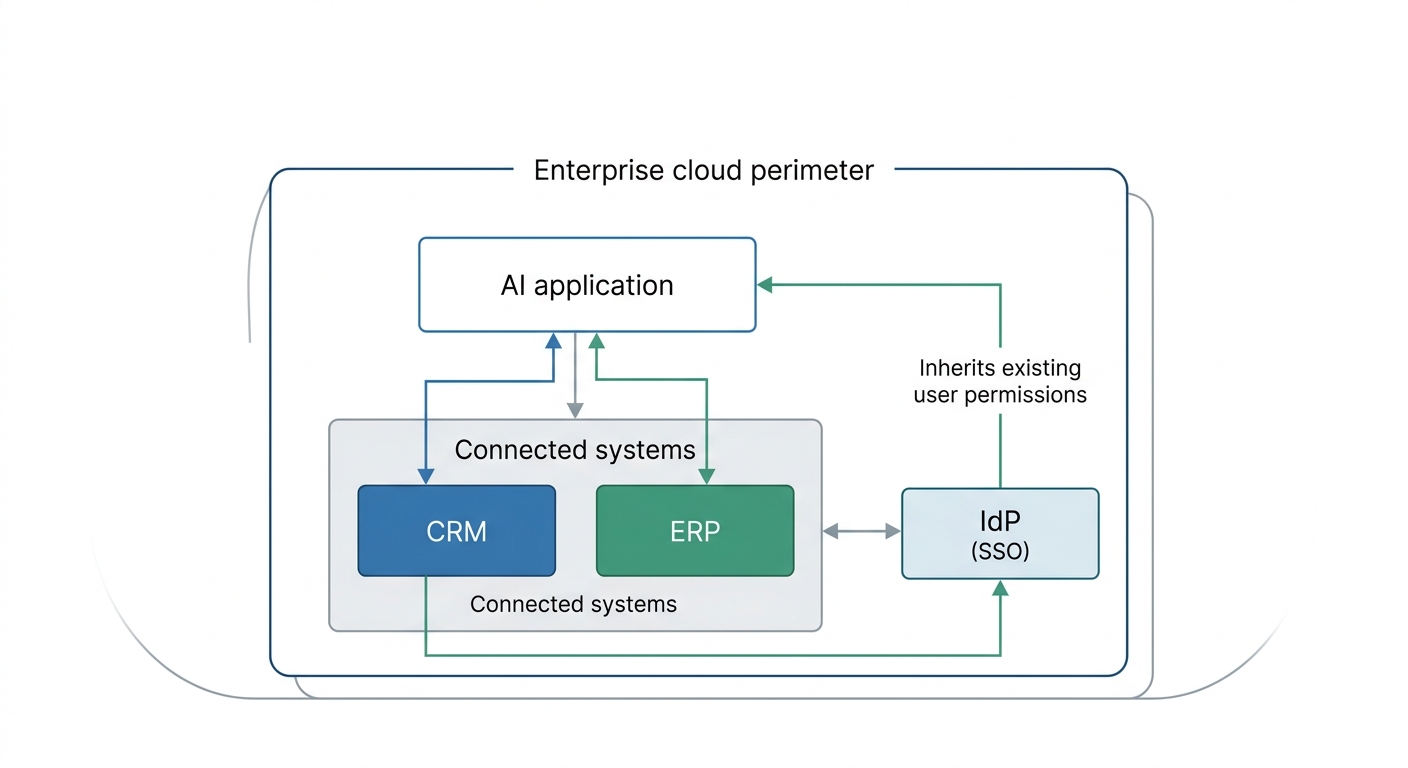
Access Parity Across Integrations
When AI connects to third-party systems — CRMs, data warehouses, ERPs, collaboration tools — it inherits the exact permissions the user already holds in those systems. Nothing more, nothing less. A user who can read-only a Salesforce record cannot write to it through an AI interface. This principle of access parity ensures that connecting an AI layer to existing systems doesn't create a new privilege escalation vector.
Encryption and Zero Data Leakage All tokens and conversation data are encrypted at rest in the customer's own database. Critically, data is never used to train external models — a non-negotiable requirement for enterprises handling proprietary, confidential, or regulated information.
ROI & Business Value
| Outcome | Business Impact |
|---|---|
| Eliminated shadow AI risk | Reduces unauthorized AI tool adoption by giving teams a sanctioned, secure alternative |
| Accelerated security review cycles | Governed architecture shortens procurement and security approval timelines |
| Regulatory compliance confidence | Data residency and audit trails support HIPAA, SOC 2, GDPR, and similar frameworks |
| Reduced IAM overhead | IdP integration means no separate AI user management burden on IT |
| Zero privilege escalation surface | Access parity eliminates a new class of security vulnerability |
| Faster AI ROI realization | Teams can deploy AI use cases without waiting months for security sign-off |
Practical Implementation Guide
Follow these steps to deploy enterprise AI within a governed security framework:
Map your data classification tiers first. Before deploying any AI tool, identify which data categories (PII, financial, IP, confidential) will potentially interact with AI workflows. This determines your compliance requirements upfront.
Select a deployment model that keeps data in your environment. Prioritize architectures that run within your existing cloud account (AWS, Azure, GCP) rather than third-party SaaS infrastructure. Validate where conversation history and embeddings are stored.
Connect to your existing Identity Provider before onboarding users. SSO integration should be the first configuration step — not an optional feature added later. This ensures access governance is enforced from day one.
Establish OAuth-governed integration connections. When connecting AI to business systems, use OAuth flows that inherit existing user permissions. Audit the permission scopes being granted and document them for compliance review.
Implement PII detection and data guardrails. Configure automated scanning of inputs and outputs to detect and redact sensitive data before it reaches language model APIs. Treat this as a mandatory control, not a nice-to-have.
Define role-based access policies for AI capabilities. Not every user should have access to every AI tool or knowledge source. Map AI access tiers to existing organizational roles using the same RBAC model you apply elsewhere.
Enable audit logging from the start. Every AI interaction should produce a tamper-evident log tied to a specific user identity, timestamp, and data source accessed. This is essential for compliance investigations and incident response.
Run a security review against your existing frameworks. Bring your CISO or security team into the deployment process with documented evidence of data residency, encryption standards, and access controls — treat it like any other enterprise software procurement.
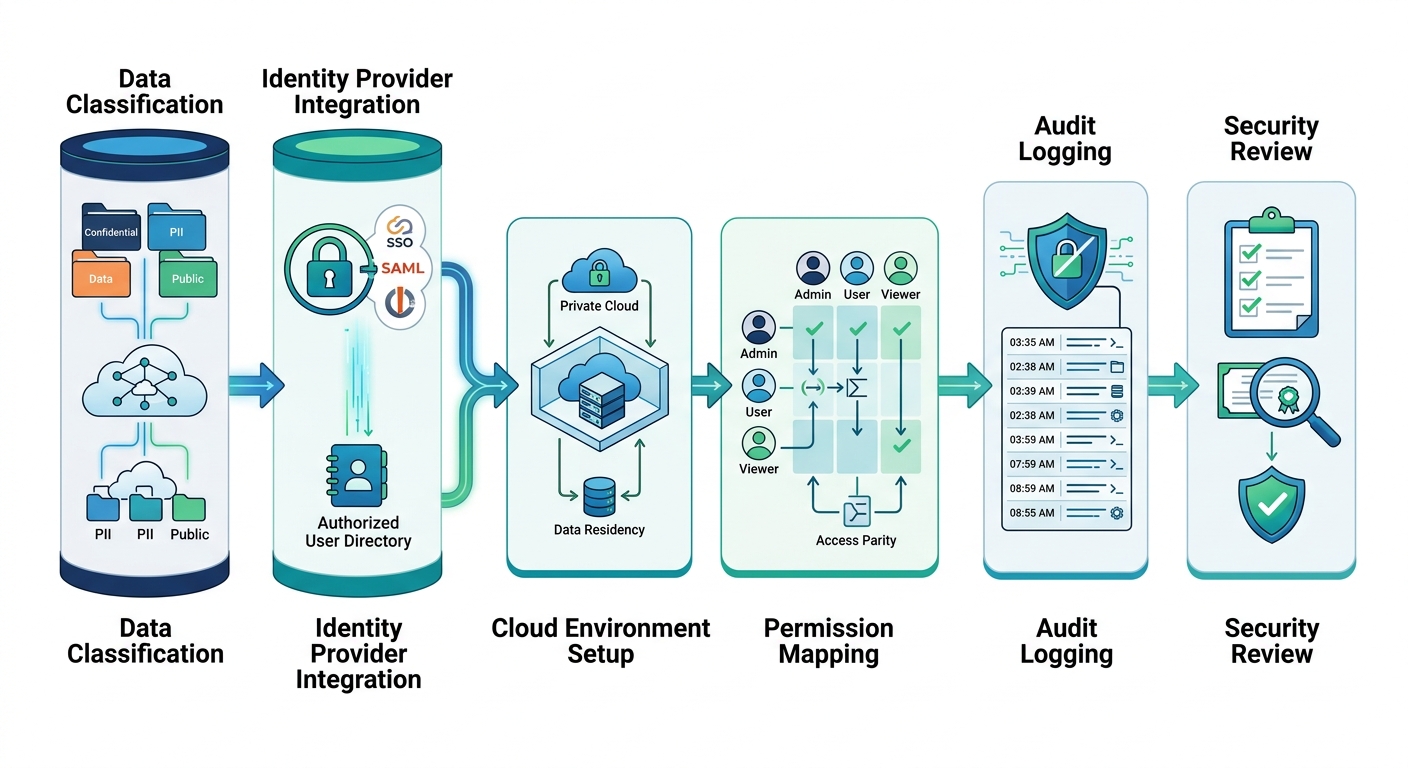
A sequential workflow diagram starting with data classification and identity provider integration, moving through cloud environment setup and permission mapping, and concluding with audit logging and final security review.